За последний год российские компании столкнулись с сильным всплеском DDoS-атак. По оценкам нескольких независимых источников, с 2021 по 2022 их число увеличилось в 8 раз. Мишенью становятся разные проекты — от крупных IT-сервисов и приложений до сайтов небольших компаний и трансляций онлайн-мероприятий. Чтобы данные ваших пользователей были в безопасности, а сервер работал без перебоев, используйте многоуровневую систему защиты.
Защита от атак из списка OWASP TOP 10
Предотвращение бот-активности (DNS/JS проверки, BOT-сигнатуры, анализ поведения браузеров)
Пассивный сканер уязвимостей
Защита от client-side атак (CSP, CSRF injection)
Защита от Credential stuffing
Предотвращение подбора учетных записей
Предотвращение поиска скрытых директорий сайта (DirBuster)
AntiDDoS
Преимущества LINX Protect
Экономия ресурсов
Эксперты Linx берут на себя внедрение, эксплуатацию и поддержку продукта. Ваши ИТ-специалисты могут сфокусироваться на ключевых бизнес-задачах вашей компании
Снижение нагрузки на вашу ИТ-инфраструктуру
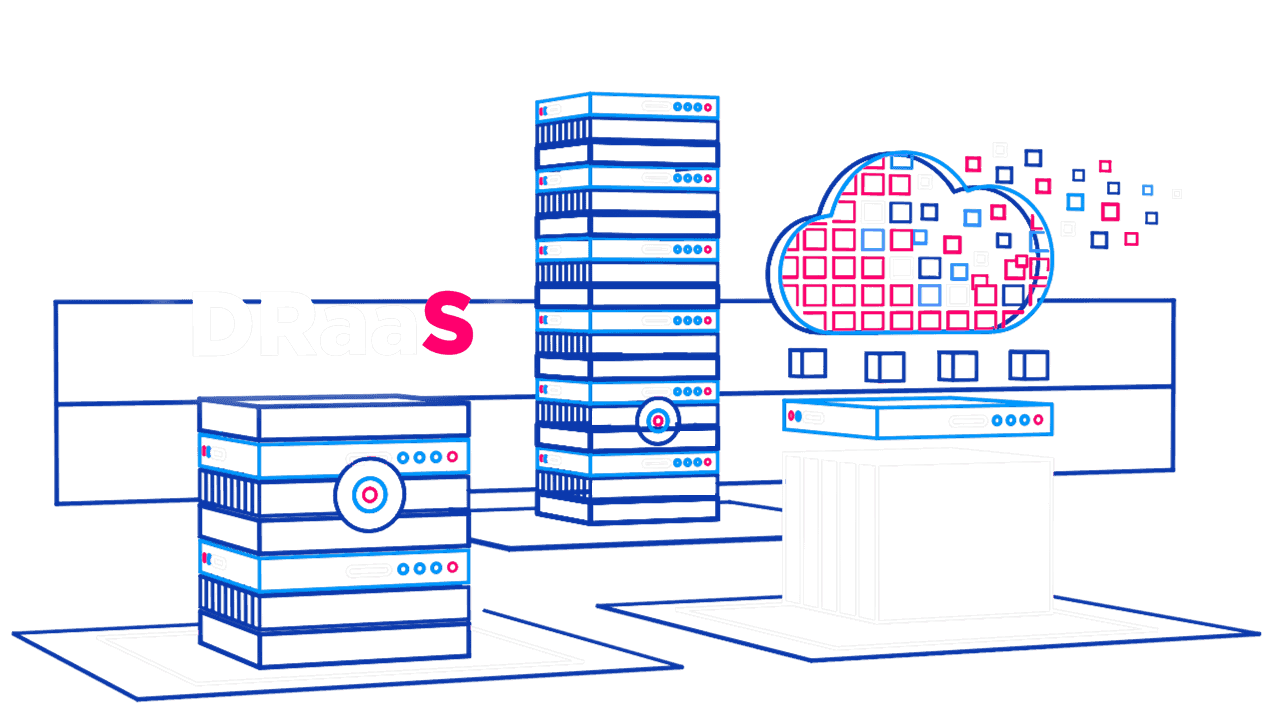
Продукт работает полностью в облачной среде и освобождает ваши ИТ-ресурсы от излишней нагрузки. Механизмы защиты позволяют выявить ботов и заблокировать их, не нарушая работу легитимных пользователей
Актуальные политики защиты
Собственная сеть ловушек (honeypot) позволяет получать информацию о новых векторах атак из даркнета и создавать актуальные сигнатуры и политики безопасности
Точность 99,9%
Минимум ложных срабатываний при анализе входящего трафика благодаря регулярной аналитической работе команды Linx
круглосуточный мониторинг
Оперативное реагирование на инциденты в режиме 24/7
Простота подключения
Достаточно перенаправить трафик с помощью DNS-записи на Linx Protect
Цель DDoS-атаки — вывести оборудование из строя. Это могут быть конкуренты, которые хотят вывести из строя вашу платформу, навредить репутации или продажам, а могут быть хакеры, которые ищут уязвимые места. Вне зависимости от задач, технология одна:
- На сервер отправляются вредоносные запросы.
- Его мощности не выдерживают.
- Он падает.
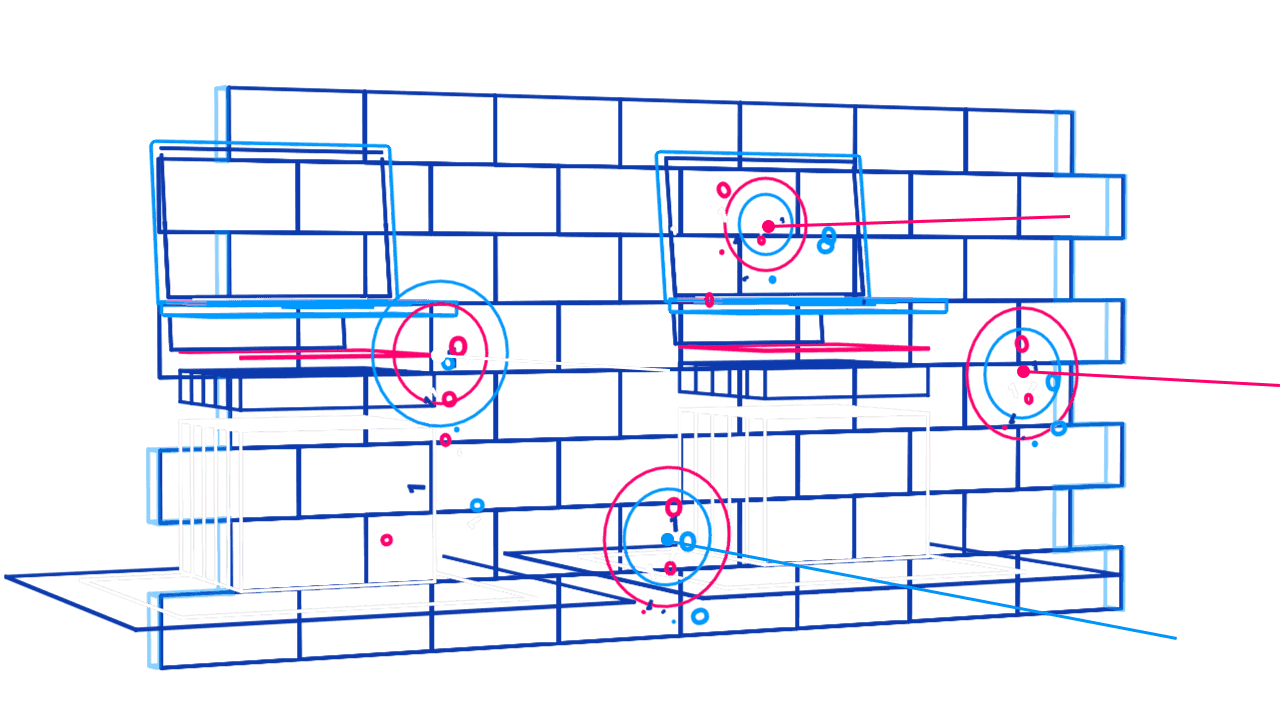
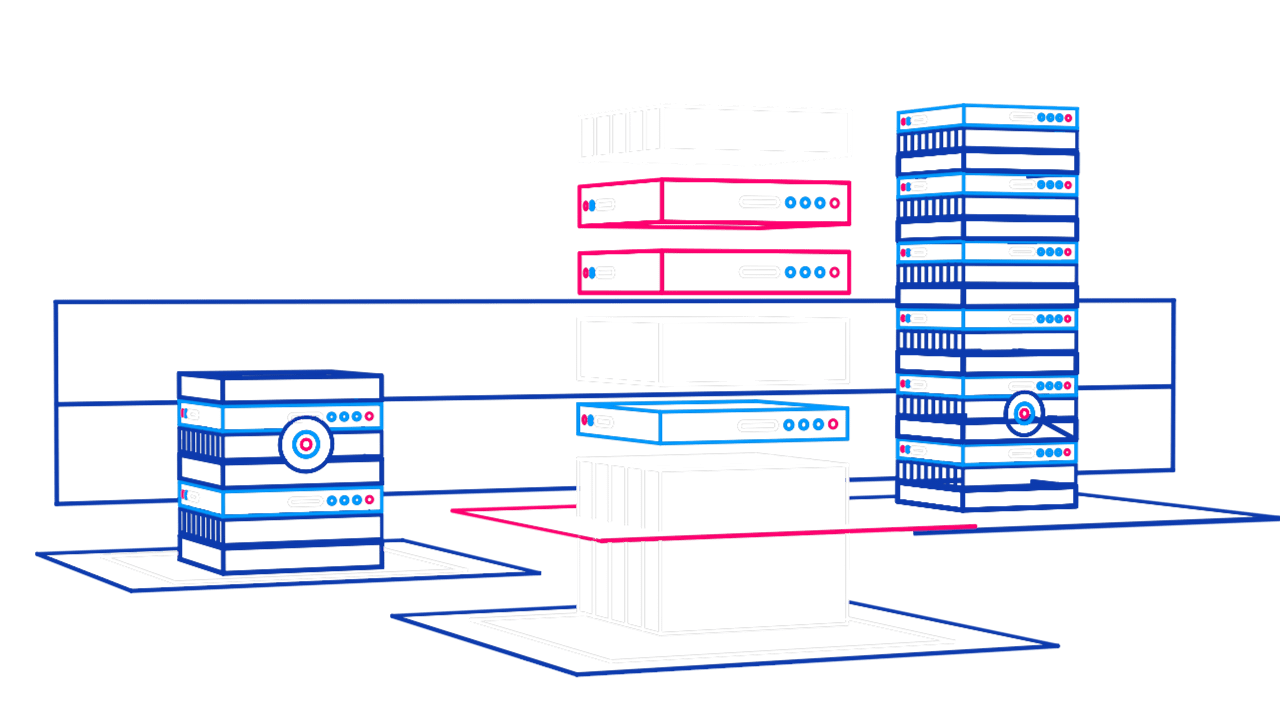
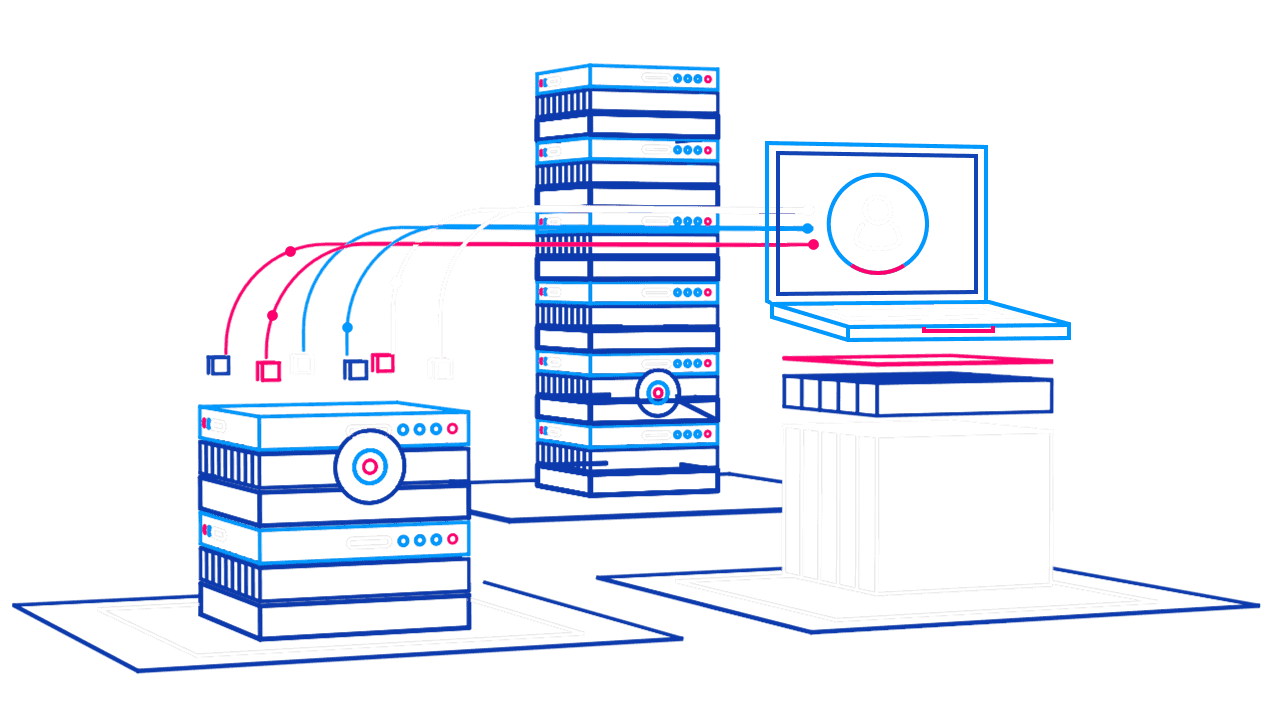
У каждого провайдера свои алгоритмы, но защита всегда строится на фильтрации трафика. Система направляет запросы на промежуточные адреса, прогоняет его через специальное оборудование и внутренние сервисы для очистки. Вредоносные запросы отбрасываются, а на сервер направляется очищенный трафик.
Для усиления безопасности Linx Cloud использует несколько технологий — пассивный сканер уязвимости, облачные сервисы, которые позволяют запускать мощные алгоритмы проверки, файервол веб приложений WAF для анализа трафика и т.д. В совокупности они позволяют поддерживать высокий уровень защиты от большинства видов атак.
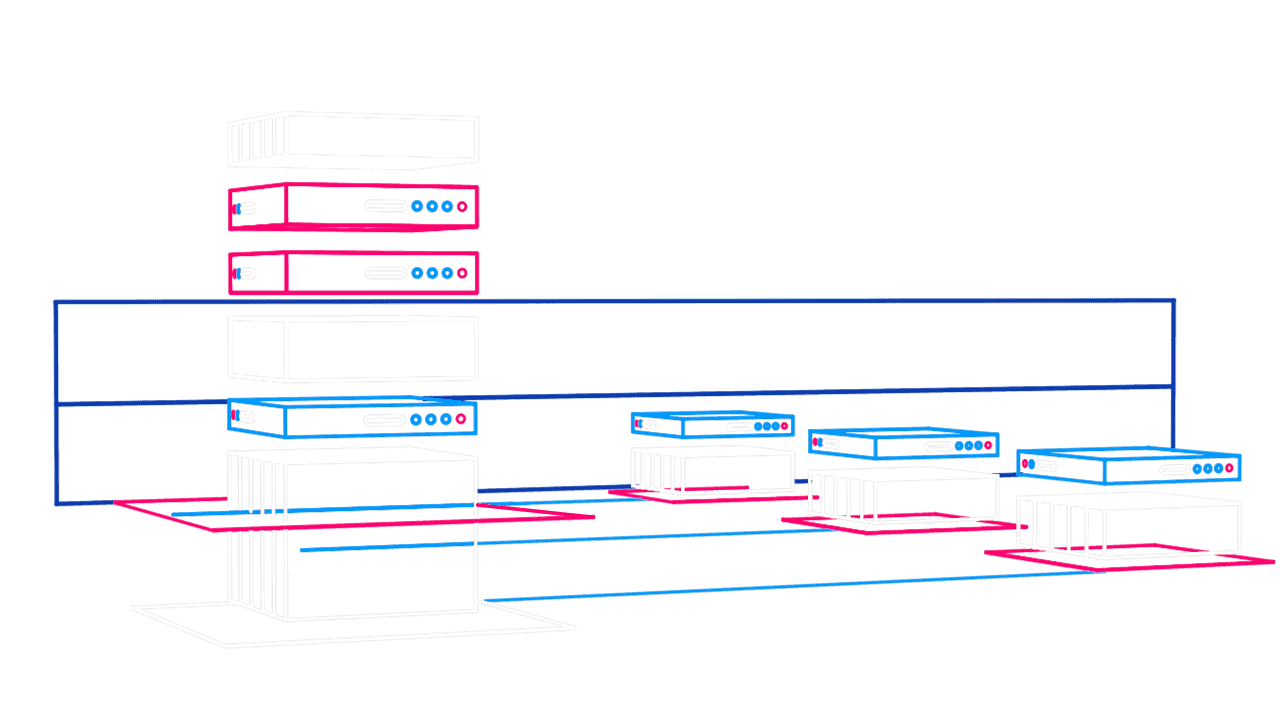
Архитектура системы защиты от атак
Тарифы
Базовый
3544 ₽/сутки
- 1 домен (приложение)
- AntiDDoS - 10 Мбит/с
- WAF - 100 RPS
- Фильтрация трафика на уровнях 3-5 модели OSI
- Сигнатуры OWASP
- Полное обслуживание WAF, мониторинг и реагирование на инциденты
- Консультации по уязвимостям и инцидентам
Стандарт
4428 ₽/сутки
- 3 домена (приложения)
- AntiDDoS - 30 Мбит/с
- WAF - 200 RPS
- Фильтрация трафика на уровнях 3-5 модели OSI
- Сигнатуры OWASP
- Полное обслуживание WAF, мониторинг и реагирование на инциденты
- Консультации по уязвимостям и инцидентам
Бизнес
6500 ₽/сутки
- 10 доменов (приложений)
- AntiDDoS - 100 Мбит/с
- WAF - 400 RPS
- Фильтрация трафика на уровнях 3-5 модели OSI
- Сигнатуры OWASP
- Полное обслуживание WAF, мониторинг и реагирование на инциденты
- Консультации по уязвимостям и инцидентам
Индивидуальный
Подберем под ваши потребности
часто задаваемые вопросы
Если сайт — центральное звено маркетинга компании и через него проходят большие потоки трафика, то базовая защита от DDoS атак обязательна. С проблемами сталкиваются разные интернет-сервисы, у которых есть недобросовестные конкуренты. Особенно страдают веб-приложения, у которых монетизация напрямую зависит от работы платформы, и онлайн-трансляции мероприятий, где на кону репутация организаторов.
Другие мишени DDoS:
- Платежные системы.
- Государственные ресурсы.
- Медиа.
- Медицинские сервисы.
- Интернет-магазины.
- IoT оборудование.
- Биржи криптовалют.
- Корпоративные сайты.
Даже если вашего проекта нет в списке, это не гарантирует полную безопасность, поскольку более 60% компаний ежемесячно страдают от DDoS.
Это не совсем так. Задача атаки — вывести оборудование из строя, чтобы помешать нормальной работе сервиса. Однако нередко это нужно для отвлечения внимания, пока хакеры пытаются взломать вашу базу данных, которая хранится на сервере.
Вы можете заказать услугу в личном кабинете. При необходимости тариф легко меняется в интерфейсе — цена зависит от мощности требуемой защиты. С технической точки зрения, вам нужно добавить DNS-запись, которая будет направлять трафик.
Ваши пользователи не заметят изменений — скорость остается той же. Комплексная защита, наоборот, становится подмогой для сервера. Фильтры снижает нагрузку на него, поэтому приложения работают быстрее.
Чаще всего DDoS бывают двух типов:
- На уровнях L3, L4 (инфраструктура) — к ним относится работа с разными типами сетевых и транспортных протоколов, в частности IP, SYN и UDP-флуд. Они действуют как перегрузка и их легко обнаружить даже с помощью самой простой системы.
- На уровнях L6, L7 (приложения) — их сложнее распознать, поскольку они не настолько массированные и направлены на отдельные части приложения. Для отражения этого типа атак мы используем WAF.
Мы обеспечиваем безопасность для сервера как при стандартном флуде, так и при «интеллектуальных» атаках, когда запускают продвинутых ботов. Существуют более сложные кибератаки, которые включаются в рейтинг OWASP TOP 10. Это самые опасные алгоритмы, которые могут с помощью специальных запросов вытягивать данные из вашей базы, проникать на сервер с полным доступом, используя ваш IP, и использовать другие уязвимости в корыстных целях. Наш комплекс включает решения по борьбе с подобными вмешательствами.
Да, все наши сервисы и облачные решения подходят под требования закона о персональных данных. Оборудование расположено в дата-центрах Москвы и Санкт-Петербурга.